The Security Snapshot
See what attackers already know about your organisation before they use it, delivered in 5 working days.


They begin with what they can see.
✓ External services
✓ Forgotten assets
✓ Exposed technologies
✓ Misconfigured platforms
Without independent visibility of your external footprint, unknown exposure can become the starting point for security incidents.
The Security Snapshot provides a structured, independent assessment of what is publicly visible about your organisation and the risks this exposure presents.
✓ Delivered in 5 working days
✓ No internal access required
✓ No operational disruption
The Security Snapshot gives organisations a clear understanding of their external security posture, helping both technical teams and leadership identify exposure and prioritise action.
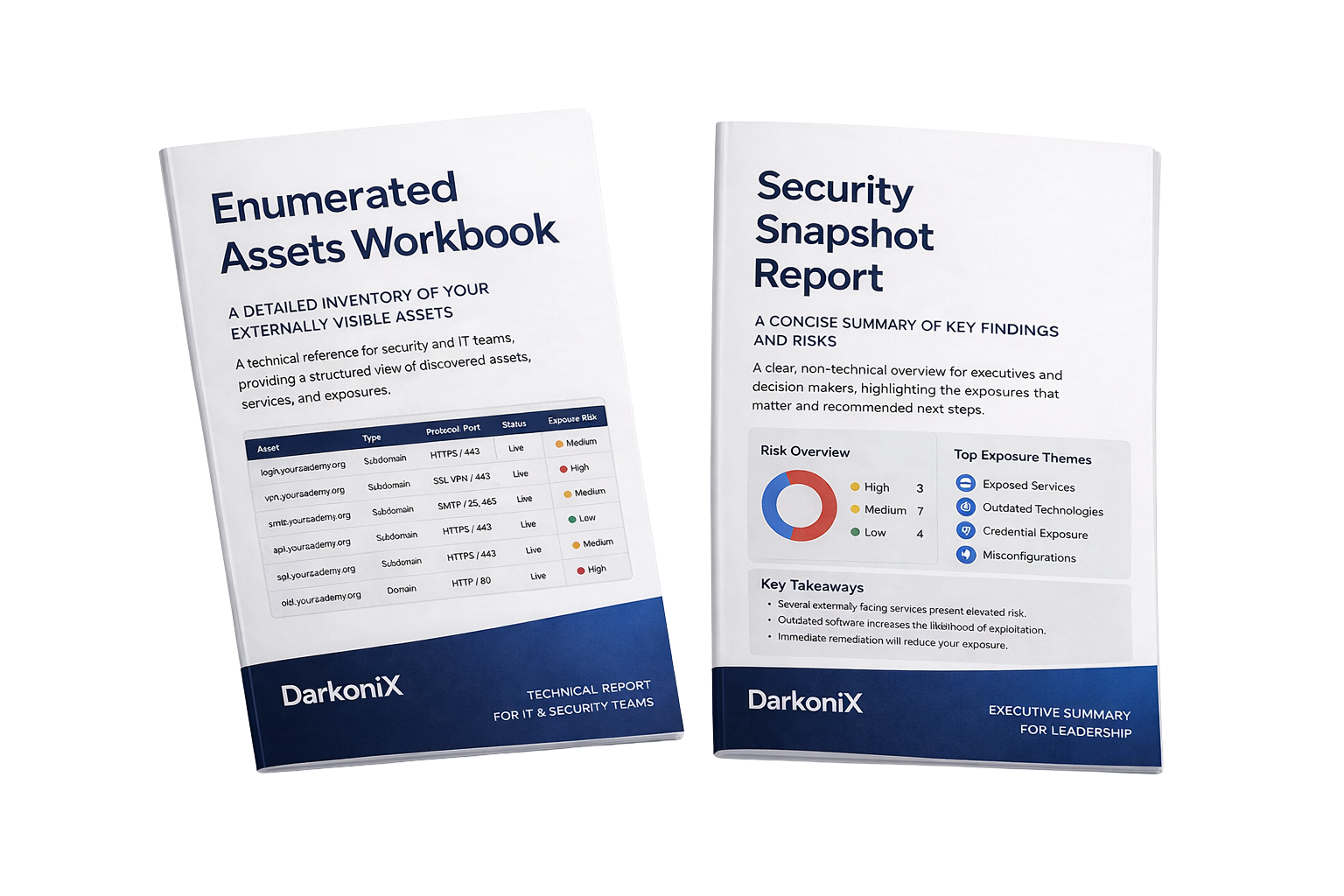
Through two focused outputs, the service provides both technical depth and executive clarity.
Together, they provide a complete, practical view of external exposure and recommended next steps.
Your complete external asset inventory.
A clear list of websites, domains, and externally accessible services connected to your organisation. Shows what is official, what is third party managed, and what exists online under your organisation's identity.
Provides technical teams with visibility of:
✔︎ Discovered domains and subdomains
✔︎ Externally exposed services
✔︎ Third party platforms
✔︎ Technology and hosting indicators
✔︎ Potential exposure risks
Your executive level exposure assessment.
A concise, leadership friendly summary of key observations, exposure themes, and potential risks. Built using the DarkoniX external security scoring model to help organisations understand their external exposure and prioritise improvement.
Provides organisations with:
✔︎ External exposure grade
✔︎ Dimension based exposure scoring
✔︎ Identified external risks
✔︎ Business risk context
✔︎ Priority improvement areas
✔︎ Clear recommended next steps
Within 5 working days, our structured four step process provides organisations with an independent view of their external exposure.